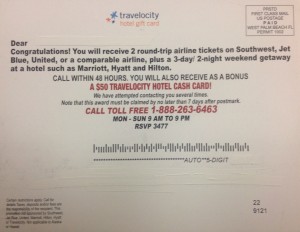
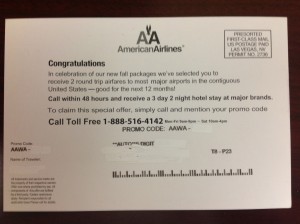
A few months ago, as most of us trudged through the gray days of winter, I wrote about the “American Airlines Fly Away Promotion” postcard scam I’d received in my snail mailbox during the holidays. I didn’t bite on that offer but I’m happy to report, with Spring Fever upon us, I’ve got another chance at a fabulous vacation—for FREE! Just this week, I received another incredible notification on a postcard. This one had a slightly different twist because it was from “Travelocity hotel gift card!” Here’s what it said…
Congratulations! You will receive 2 round-trip airline tickets on Southwest, Jet Blue, United, or a comparable airline, plus a 3-day/2 night weekend getaway at a hotel such as Marriott, Hyatt and Hilton.
This postcard also included a picture of a commercial jet airplane — this one was a Boeing 747 – adorned with the Travelocity name and logo. It instructed me to,
Call within 48 hours. You will also receive as a bonus a $50 Travelocity Hotel Cash Card!
All good stuff, but I needed to act quickly this time, according to the card. It said they had attempted to contact me several times and that this award must be claimed no later than 7 days after postmark. I must have missed their message on my answering machine and my caller ID failed to record the missed calls from Travelocity or the phone number provided, 1-888-263-6463.
Luckily, I got the postcard in time! “Hot Diggity!” This offer was even better than the first one because twice they used words like “will,” which sounds like a guarantee to me! I’m thinking my next vacation is all but a done deal. Heck, I don’t even care if I have to sit through a 90-minute travel club presentation to claim my prize. I’m OK with that, especially since I have more time than money. I’m willing to sit through a short sales presentation in exchange for saving hundreds of dollars on plane tickets. Then I’m booking my seats on that “Freedom Bird” baby! And the tickets are FREE!
F – R – E – E !…Right?
Well, they’re free after I pay the applicable taxes, deposits and/or fees, which are usually about $100 per ticket. But once I’ve done that, I can fly almost anywhere, whenever I want. In the words of Lynyrd Skynyrd, I’ll be free as a bird, now…”
…except not during the blackout dates or other restricted times and if those times are already full.
But even if this prize/promotion isn’t actually sponsored by Travelocity, what’s the big deal with that? Just like the other postcard notification, they were honest enough to provide that information in the fine print, as follows:
Certain restrictions apply. Call for details. Taxes, deposits and/or fees are the responsibility of the recipient. This promotion not sponsored by Southwest, Jet Blue, United, Marriott, Hilton, Hyatt or Travelocity. Not
applicable to Alaska or Hawaii.
ALL RIGHT! ENOUGH ALREADY! It’s time to stop kidding myself, trying to convince myself that this is a good deal for me. And you should stop trying to convince yourself, too. THIS IS A RIPOFF!
If we’re being honest with ourselves, we’d be better off just round filing that postcard if ANY of the following apply:
- You’re told that you must provide personal information, such as your age, marital status, or household income in order to be eligible for the prize or promotion.
- There’s a charge for anything you’ve won.
- More conditions or requirements arise as you move along in the process.
- You encounter hard-sell tactics pressuring you to join a costly travel club.
- Special deals, rates, or vacation packages are good for a limited time or one day only, creating a sense of urgency for you to quickly make a decision to purchase.
- The representative on the phone informs you there will be a “small service fee applied to your card” for accepting the prize or special offer.
- The old “ Bait & Switch” occurs, where you’re told about the “catch” after you’ve provided your credit card information, such as a requirement to buy an additional ticket or night’s stay at the regular (often inflated) price in order to get the freebie.
- You’re told you will have an opportunity to review the vacation package before your credit card is actually charged, when in fact, your card is charged immediately.
If you do take a company up on their vacation offer, be aware of these red flags:
- The charges add up to more than the cost of the airfare and hotel had you purchased them on your own.
- For the discount travel package all you receive are coupons or discounts you could obtain elsewhere for free.
- Your vacation materials are slow to arrive in the mail, if they arrive at all.
- The promised materials do arrive in the mail but not until after the booking period has passed or possibly not until after the “review period” has elapsed.
Finally, take these precautions ahead of time:
- Directly contact the company whose name appears on any promotion (Travelocity in this case) to verify that they are, in fact, offering the promotion or prize.
- Don’t sign any agreements that don’t spell out all of the promised services and conditions for obtaining them.
- If you do provide a credit card, debit card, or bank account number, for ANY reason, expect to be charged. DO NOT provide the information until after all of your reservations are confirmed, in writing, with a reservation number.
You can ask all the questions you want to about cancellation policies and the availability of trip insurance, but if you’re dealing with scammers, fraudsters, liars, or thieves, they’ll tell you EXACTLY what you want to hear, and they’ll take more of your money to do it. Victims of vacation scams don’t usually discover they’re being taken until they try to make their reservations, only to find out they cannot reach the “travel agency” because their phones are disconnected, the company has moved, or it’s out of business altogether. And of course, the travel company didn’t contact them to notify them of these “unfortunate circumstances” or to offer a refund.
BOTTOM LINE: Be very wary of any vacation or travel “prize” or “award” – especially from a contest or promotion you didn’t enter or other unsolicited source. Don’t be like the facetious me above and ignore the warning signs just because you really want to be a “winner!” Shred those “Stay-Away-Cation” postcards and save your time and money, while avoiding the headaches.
Other Related Articles:
Free Vacation Give Away Scams
Scammers Lure Victims with Fake Free Plane Tickets
If you're looking for great anti-virus software that won't break the bank, try StopSign. You don't pay extra for tech support for difficult malware, and our web protection software just works. Download & install StopSign to find out why our members choose us over the other options.









Recent Blog Comments