In the world of internet security, new versions and variants of malware appear on a daily basis, although relatively few pieces of new malware actually get notable time in the spotlight. Despite all the discussion of worms and backdoors, much of the time, new works of malware these days are designed simply to facilitate browser redirection or the serving of ads to users. Prior to this, false or “rogue” anti-virus programs saw a moment of popularity. If they happened to make their way onto a machine, these rogue anti-virus programs would claim the machine to be infected and offer to kindly cure this non-existent infection for a modest fee. In the end, these programs focused on making a minor nuisance of themselves in the name of ultimately exploiting the user to generate or increase revenue, or direct web traffic to a particular site.
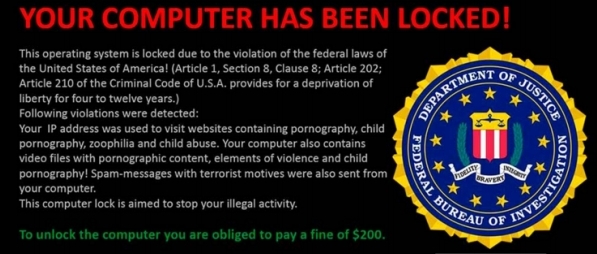
Every now and then, however, something truly worthy of pause surfaces. The big news in the realm of internet security over the past several weeks has been the appearance of Cryptolocker, a new entry into the category of malware frequently referred to as ransomware. Like many other types of malware, ransomware also aims to generate revenue, but its approach takes a critical diversion from nuisance, opting instead to restrict access to the computer in some way and holding the machine hostage under the demands of a ransom. Until recently, the most successful ransomware usually involved hijacking the desktop, generally under the guise of a law enforcement agency such as the FBI, the machine left in a state where the user is presented with a demand. In these cases, the machine and its contents are left intact, although the user is unable to use the machine until the infection is removed or the ransom paid.
Removal of these particular forms of ransomware were occasionally time consuming, but once fully removed, the machine was left in the same state it was prior to being infected, negating the need to pay the ransom.
Enter Cryptolocker
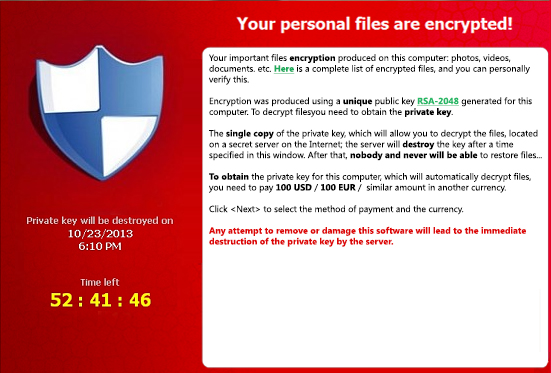
Cryptolocker takes what seems to many to be the next obvious step, leaving the machine largely accessible to the user but encrypting their documents. Cryptolocker is most often seen distributed via email. Upon installing itself onto the machine, Cryptolocker begins searching through the enumerated drives looking for various documents to encrypt. Meanwhile, it also calls a randomly selected server on the Internet to register itself and acquire an encryption key, which it uses to encrypt the documents it finds on the machine. While Cryptolocker does not take the time to look for other machines that may happen to be on the local network and thus generally won’t discover and encrypt files on network shares, it does parse files on logical drive letters. The implication of this is that any network shares a user has mapped and assigned a drive letter to is at very real risk. During this process, the user can expect to see a significant decrease in performance coupled with continuous drive activity.
Only once Cryptolocker has completed its encryption task does it make itself overtly known, displaying a message describing how to pay the ransom to decrypt the now encrypted and unusable documents. Along with this demand comes a deadline, usually somewhere between 48 and 69 hours.
During this time, if the user chooses to pay the ransom, Cryptolocker then downloads the private key necessary to decrypt the encrypted files and slowly goes through the list of files it encrypted to restore them to their pre-encryption state.
If the user opts to not pay the ransom, the deadline issued by Cryptolocker is still of particular interest in this situation as Cryptolocker takes the effort to completely uninstall itself upon expiration of that deadline. On the surface, this may sound like an unusual effort as it means the user need only sit and wait several days, at which time their machine will clean itself. Unfortunately, this is part of Cryptolocker’s last revenge upon the user for not paying the ransom. While Cryptolocker does indeed uninstall itself, it does not take the time to decrypt the user’s encrypted documents on its way out the door. Because of the nature of the encryption used by Cryptolocker, brute force decryption of the user’s documents is not particularly feasible as it is very likely the process would take longer than the user’s lifespan. Attempting to reinstall Cryptolocker is also not a feasible option for the user as Cryptolocker generates a new set of encryption keys at that time, invalidating the previous set.
When it comes to ransomware, Cryptolocker is fairly unique in this respect as it means once a machine is infected, cleaning the infection can be disastrous to the user as it eliminates the possibility of paying the ransom for the key necessary to decrypt the documents. Once Cryptolocker has been removed from the machine, the only realistic means of recovering data from the encrypted documents is to restore them from a backup. Unfortunately, recent studies have shown that roughly half of all regular computer users not only don’t routinely back up their data but have, in fact, never created a backup of their data. Those users who do back up their data often do not do so frequently and consistently. To complicate matters even further, a quick and dirty means many people use to create a backup involves simply copying documents to an auxiliary drive. While this is certainly a valid means of backing up data and is far superior to not having a backup, it is important to remember that Cryptolocker won’t hesitate to encrypt those copies as well if the drive containing them is attached to the infected computer at the time.
Although removal of Cryptolocker is included with a StopSign subscription, concern the user may not have a backup of their documents has prompted the StopSign Research and Development Team to decide to not incorporate an automated removal of Cryptolocker into the scanner. While we wholeheartedly feel a user should never have to pay a ransom to regain access to their machine or documents, the decision in this case must ultimately fall upon the user whose data is at risk. This was a hard decision, one rarely taken here, but it is a decision we believe most anti-virus and security companies have also settled upon.
It cannot be stressed enough that removing Cryptolocker effectively eliminates all data recovery options for the user other than restoring data from a backup and should never be done without the user’s consent.
How to Protect Yourself
When it comes to malware, prevention is critical. Users should always be mindful of suspicious or unexpected emails and instant messages. The StopSign Security Suite provides a powerful on-access scanner component designed to monitor the system in real time. Keeping the operating system and associated software properly updated can also be crucial in maintaining a malware-free environment.
Painless Removal
If you should find yourself facing a Cryptolocker infection, we would be happy to provide personalized assistance to quickly remove it from your machine. Our technicians are available at 1-800-786-7744 to discuss the matter with you and assist in removal.
If you're looking for great anti-virus software that won't break the bank, try StopSign. You don't pay extra for tech support for difficult malware, and our web protection software just works. Download & install StopSign to find out why our members choose us over the other options.




Recent Blog Comments