If you’re looking for a site that really puts the “social” in social media then look no further than Twitter. In our experience the majority of people on Twitter are super friendly, but every now and again you’ll run into a creep who feels it’s his or her mission in life to make you miserable, whether it’s harassing your or sending you spam. It’s usually enough to block unwanted Twitter followers, but some people step over a line and you might need to do more than just block them from your account.
We’ve come up with a list of 10 Twitter safety tips to help you avoid the less-than-scrupulous people and navigate around some of the other hassles that come with social media.
- Keep personal info personal.
Don’t share any personal information like telephone, email address, the location of your home, etc. The more you give out, the more likely you’ll find yourself with a cyberstalker, and we feel that this is an especially important Twitter safety tip. Also, be careful with any geolocation service you use (even Twitter’s own), and never tweet your location from home!
- Careful who you follow.
It’s not necessary to follow everyone who follows you. First off it’ll start to clog up your Twitter feed when you have hundreds or thousands of followers, but secondly you’ll open the door to people who are looking for an easy mark instead of a new friend. Follow, and be followed, with caution.
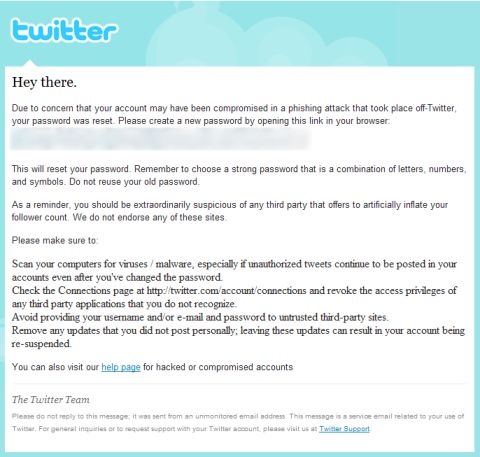
- Beware of phishing.
Phishing attacks make their rounds through DMs (or “Direct Messages”) all the time. Before you respond to a DM, make sure it’s legit.
- Only use trusted Twitter apps.
Limit which Twitter applications you use, and try to only use those which use the OAuth method of connecting to Twitter. And before you give a Twitter application a thumbs up to connect to your account, do some quick research and make sure that any app you use is reputable.
- Strong password, secure account.
Change your password regularly and use a strong password. This is probably the easiest, as well as one of the most effective, Twitter safety tips we can give.
- What did you click on?
Shortened URLs are great for keeping in the 140 characters, but that makes it harder to tell where the link takes you. Some Twitter clients, like TweetDeck, allow you to preview the destination URL before you click through. There are also several Firefox addons that will reveal the final destination of a shortened URL. And if worse comes to worse, you can always add a “+” to the end of any bit.ly URL to see its information page.
- Don’t believe everything you read.
Mama always said there’s no such thing as a free lunch, and it goes doubly so on Twitter and other social media sites. Scammers and spammers abound, and they’d love to get their hooks on you, so be wary of any offers, contests, or messages that promise the world.
- Parental guidance suggested.
Parents need to educate themselves about Twitter and pass that knowledge to their children. We recommend that parents set limits on when their children can use Twitter, as well as appropriate ages to use social media without parental supervision.
- Report threats and cyberbullying.
If you receive a threatening message on Twitter, contact your local law enforcement agencies as well as Twitter support. Cyberbullying and harassment is a growing problem online, and there’s no good reason to stand for it.
- Don’t go it alone.
A tweetup is a great way to meet local tweeps, but do it smart. Never arrange to meet someone alone in real life through Twitter. Always go with a friend, and in a public place.
Using these Twitter safety tips should help keep you less likely to be bothered with the down side of social media and enjoy the great things that Twitter has to offer.
If you're looking for great anti-virus software that won't break the bank, try StopSign. You don't pay extra for tech support for difficult malware, and our web protection software just works. Download & install StopSign to find out why our members choose us over the other options.






Recent Blog Comments